Fraud e-mails Examples
More information about blackmail and other dangerous e-mails you can found here.
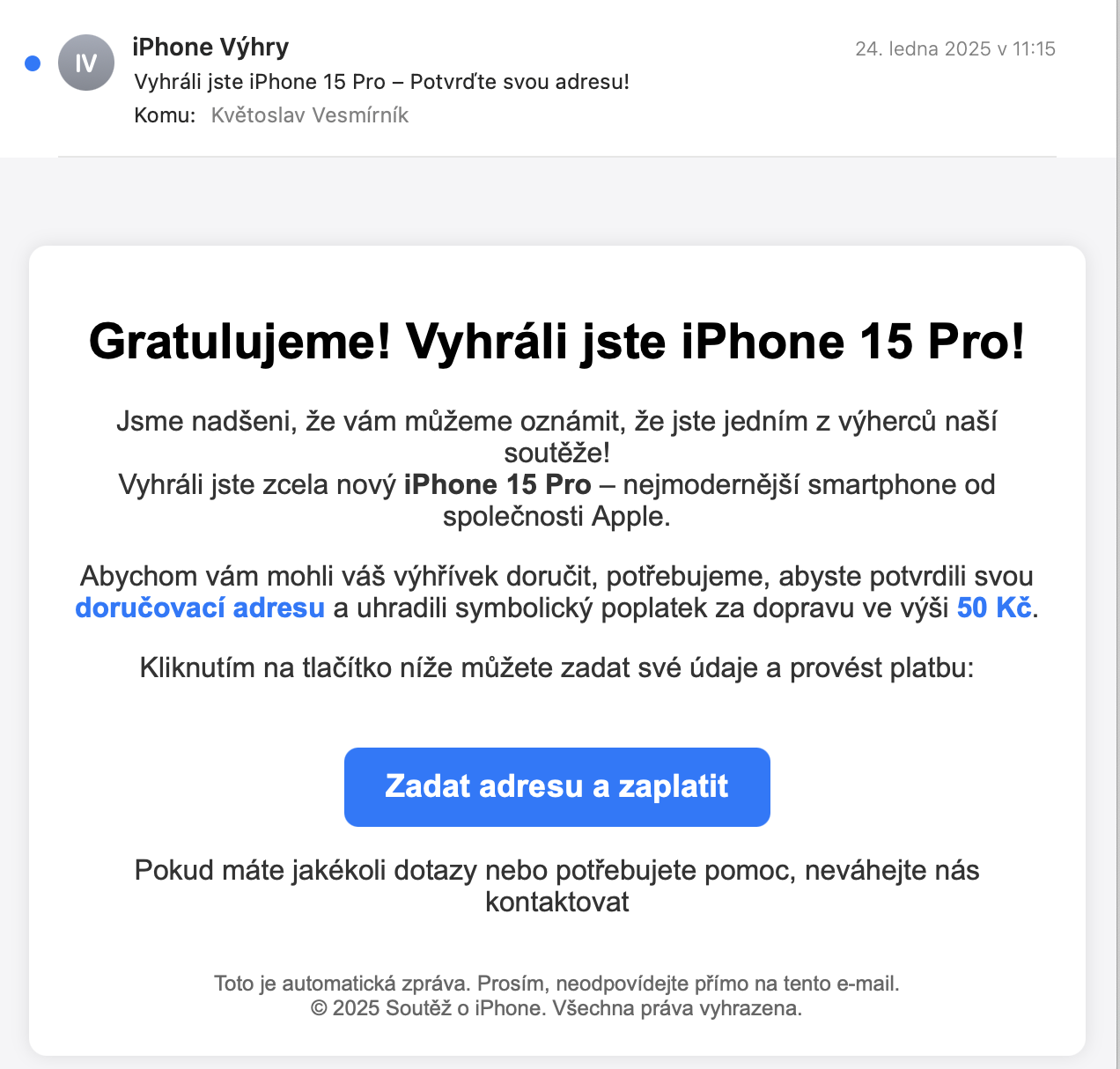
You’ve won an iPhone
2025-01-24
Attack on your wallet. You’ve reportedly won an iPhone 15 Pro!
What should stop you from doing this:
- you didn’t sign up for any lottery
- errors in Czech
- you’re supposed to pay a small shipping fee
So at first glance it looks like an attempt to extort your credit card details on the pretext of paying a small harmless fee.
You should delete the email right away!
Email:
But if you dared to click on the link, you’d get to this website:

As quickly as possible (because the last seconds tick off at the top when you still have a chance to claim the “winnings”) you’re supposed to fill in your name and address, check something written in small letters and proceed.
But if you don’t get stressed by the passing of time and read the small text under the form, you’ll find that
- there’s no more talk about an iPhone prize
- you would pay 50Kč now, but you would commit to paying an additional 928.59Kč in three days (which would probably be taken off your card automatically by now)
- and then an additional 928.59Kč every 14 days until you cancel
- you will only be able to cancel your regular payment once every 14 days, so you would not be able to cancel the first payment
- all for membership in the “loyalty club”
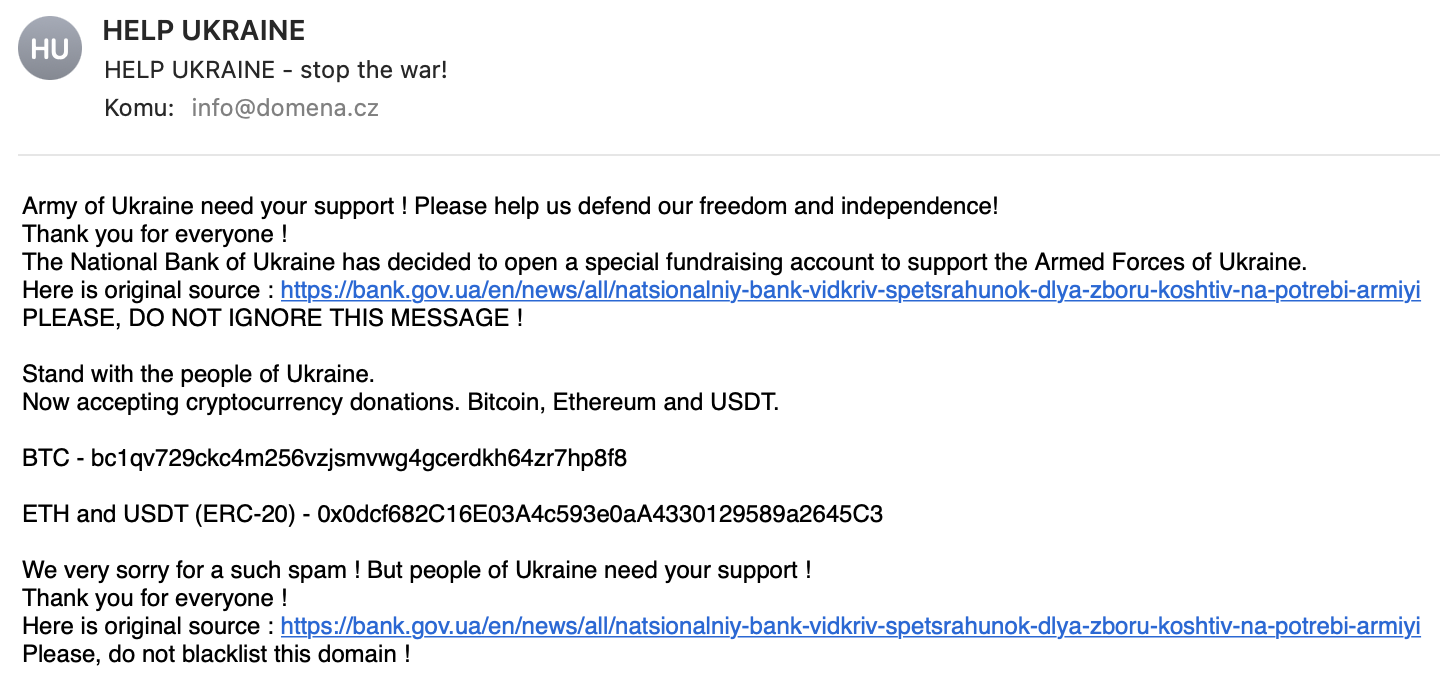
Send help to Ukraine - now you can also send bitcoins
2022-03-01
Attempt to self-enrich. The scammer refers to a real page with a call for cash support and adds “you can now also contribute in cryptocurrency.”
Signs of fraud:
- there is no mention of payment in cryptocurrency on the linked web page, the wallet address is only in the email
- according to the information in the email header it was sent from an IP address in Holland and the address is on blacklists
E-mail:
Domain expires - IMMEDIATE pay to extend it
2021-12-06
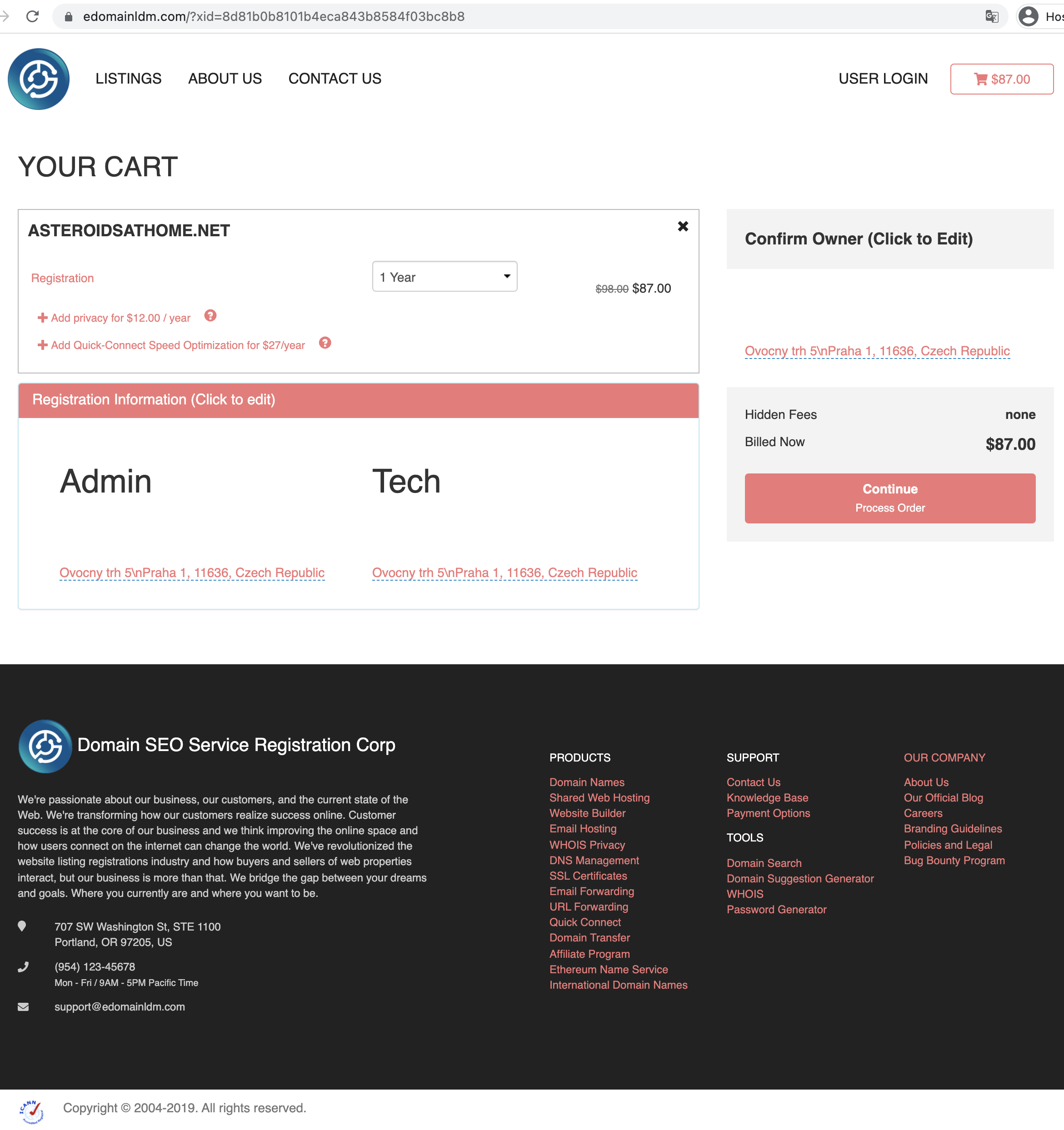
A “friendly” warning that the domain you use to present your project is expiring soon and needs to be extended immediately if you don’t want to lose it. Clicking on the link takes you to a page where you can extend your domain for a year at a price of $87 after the discount.
This is an attempted fraud. By pointing out the supposed early expiry of the domain, fraudsters try to make the recipient of the email no think and pay straight away.
If he doesn’t pay and checks first with the university domain manager, he’ll find that the domain is actually paid for four years in advance and the actual price for a 1-year extension would not be $87, but just $12, including VAT.
E-mail:
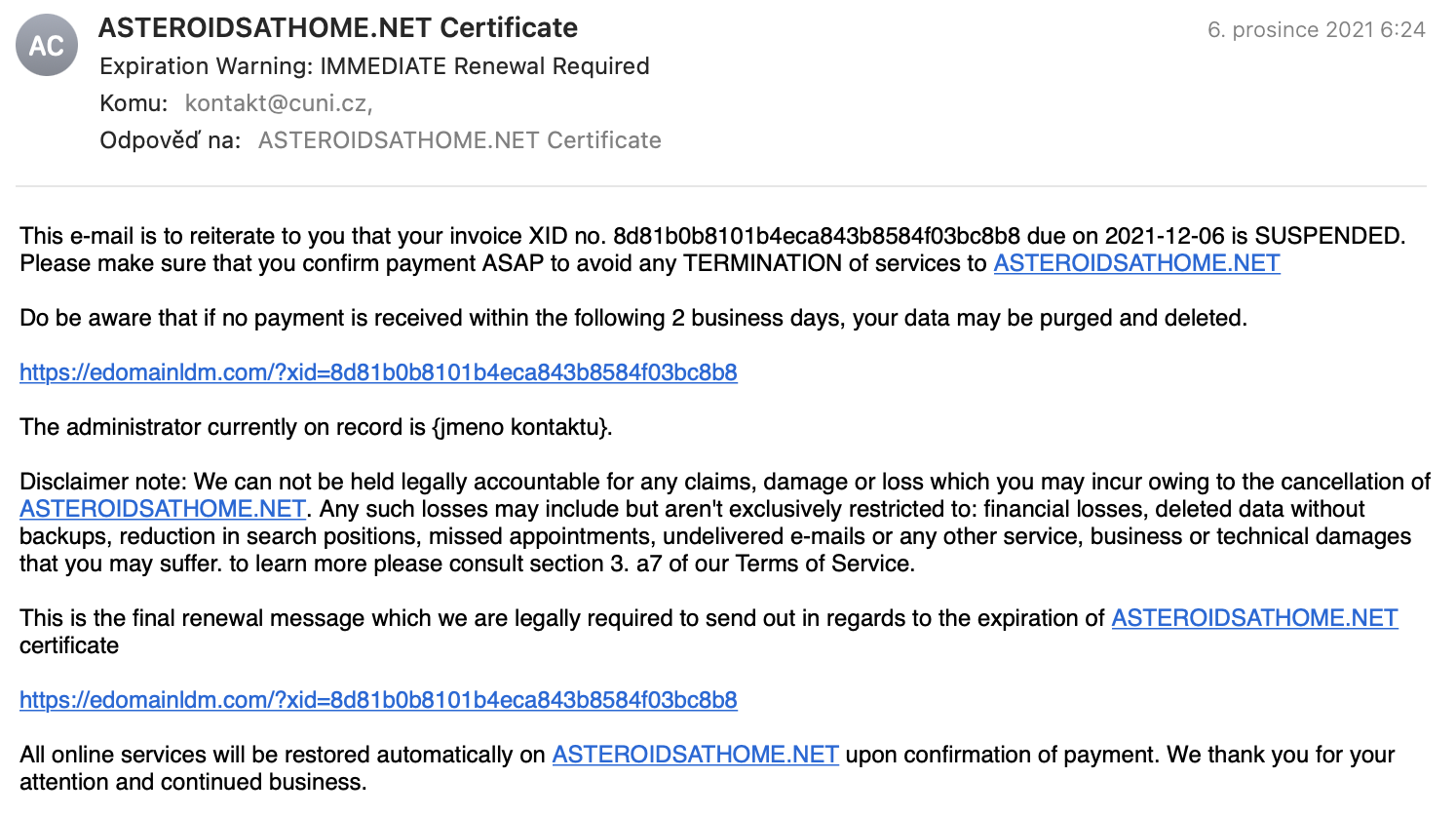
fraudster’s website:
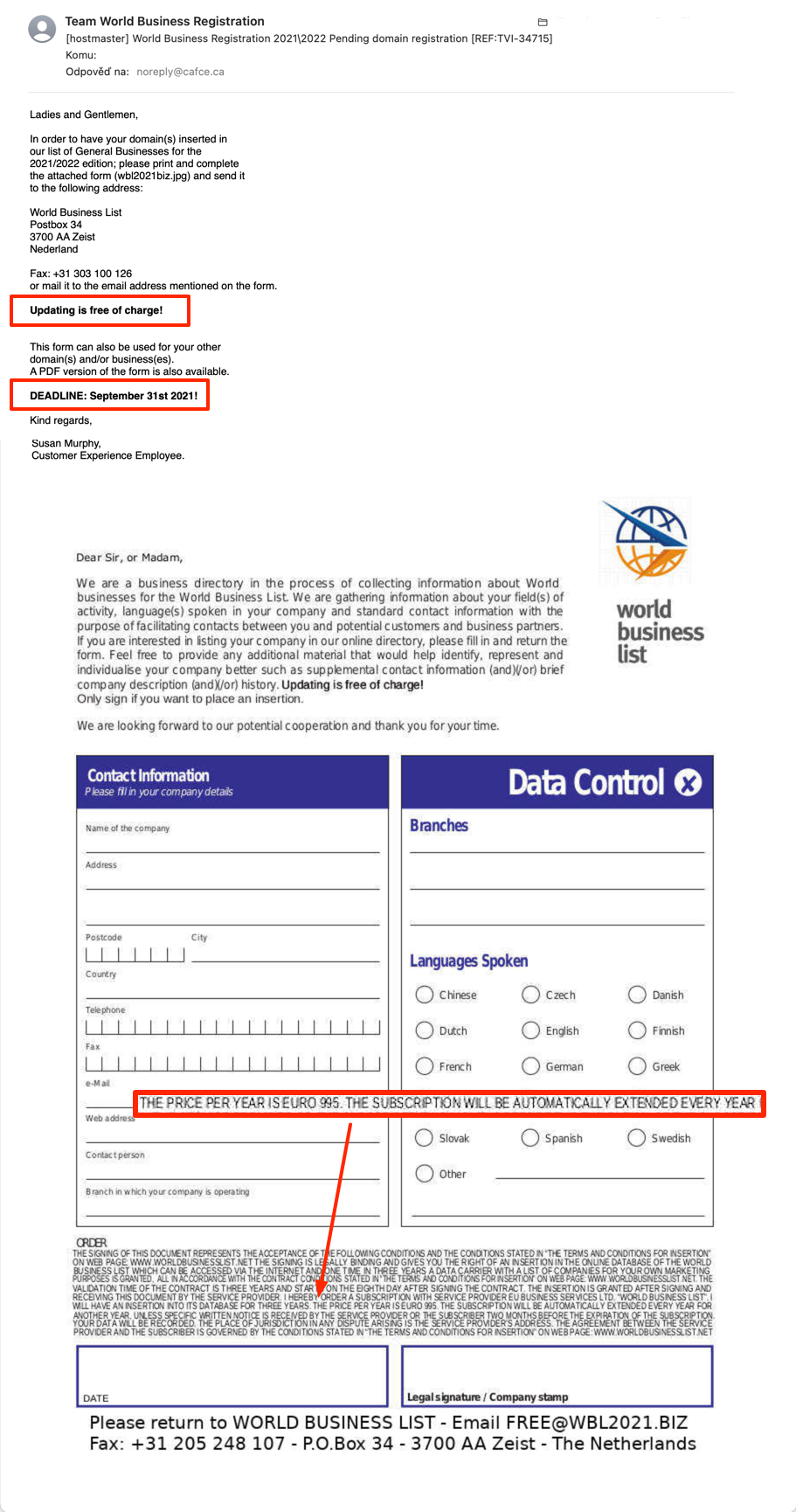
Update your details in our database
2021-08-28
Update information about your company in any database “for free”. The goal is to overlook “THE PRICE PER YEAR IS EURO 995” in the paragraph of small and unreadable text.
E-mail:
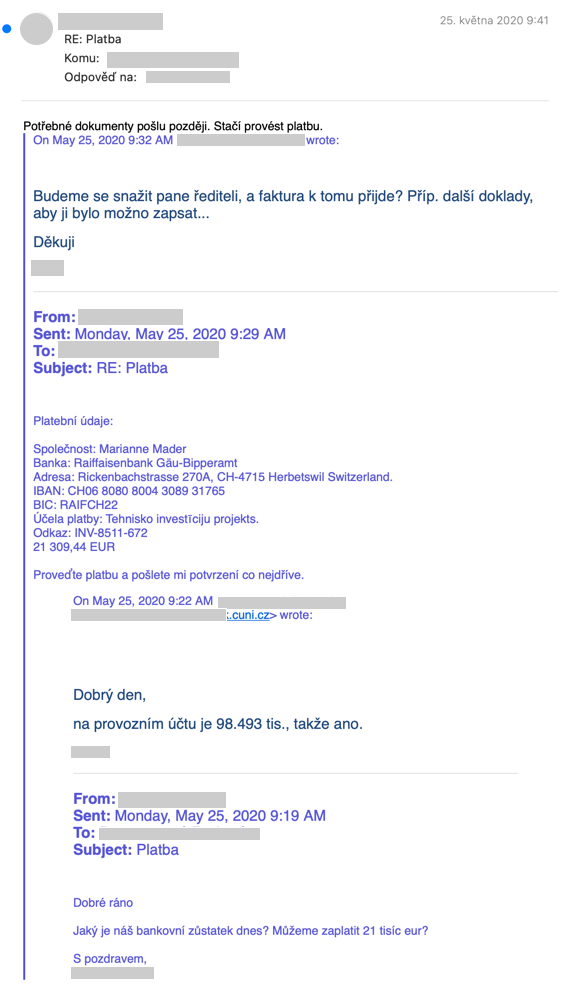
Make your payment as soon as possible
2021-05-28
Targeted attempted fraud – attacker posed as a university executive, wrote to “his” subordinates and demanded that a larger amount be sent immediately to an offshore account. The transfer did not take place, but there was a minor email exchange.
The attacker found names and contacts apparently on the web. He wrote from an address on Gmail himself and relied on it that the victim would only see the sender’s name in the Outlook and no longer the real address.
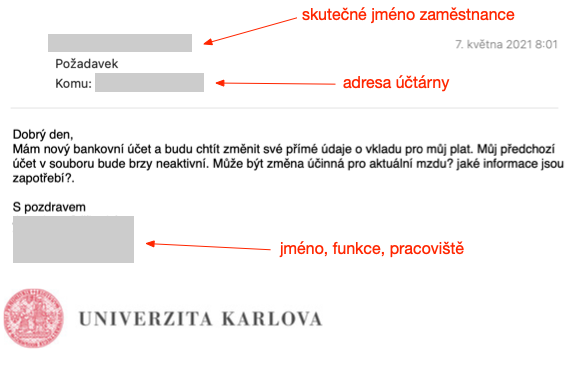
Send my paycheck to a new account number
2021-05-07
The attacker found a staff directory on the web, and a payroll accountant. He sent her an email posing as a certain real employee and tries to convince the wage an accountant to start sending paychecks to another account number.
It’s not an email sent across the board to tens of thousands of people, but one precisely targeted (and all the more dangerous for that).
The email was sent by the attacker from Gmail, where he made an account with the address chairmancommitteeeorg@gmail.com with the employee’s name and relies on Outlook only shows the name and hides the address.